The Essential Eight cyber security model: How do you measure up?
It feels like we watch cyber attacks become more sophisticated every day. Within my team, we have received emails that looked similar to legitimate company communications until we saw the sender’s address. Cyber criminals have applied the same level of sophistication to covert methods only detectable with technology.
As our workplaces become digital ecosystems full of data, the breadth of opportunities for cyber criminals to exploit vulnerabilities becomes even wider.
When protecting your organisation from cyber threats has become a necessity, how can you determine the strength of your cyber security posture?
A good place to start is by evaluating your organisation against the Essential Eight cyber security model.
What the Essential Eight cyber security model includes
The Australian Cyber Security Centre (ACSC) released the Essential Eight Maturity Model in 2015 to provide organisations with a framework for protecting their data and systems from cyber attacks. It consists of eight core protections businesses should implement to reduce their risks of experiencing an attack:
- Application control
- Patch applications
- Configure Microsoft Office macro settings
- User application hardening
- Restrict administrative privileges
- Patch operating systems
- Multi-factor authentication (MFA)
- Regular backups
What requirements might you already meet?
Many organisations rarely meet the higher maturity levels when they begin looking into the Essential Eight. You might have very few security measures in place. Or, you have strong cyber security in specific areas such as asset management but lack the necessary solutions for incident management.
In this case, you will need to focus on strengthening specific areas of your cyber security.
How the Essential Eight maturity model ranks your maturity
You might feel unsure about how you measure up regarding Essential Eight. As most businesses do not have a high maturity level when they start, they may also be unaware of potential vulnerabilities open to sophisticated attacks.
By understanding how Essential Eight ranks your company’s cyber security, you can take steps to improve your posture and protect your business from potential threats.
The Essential Eight cyber security model provides a comprehensive picture of your current posture by placing it within one of four maturity levels:
- Level 0 indicates vulnerabilities across your entire organisation. If an attacker exploits these vulnerabilities, they may compromise your data and systems.
- Level 1 aims to guard against attackers seeking to opportunistically exploit any and every organisation through publicly available internet platforms. For example, sending out ‘spray and pray’ phishing attacks hoping to gain access to a system and launch malicious applications or tamper with data.
- Level 2 protects against attackers spending concentrated efforts on a target. They may attempt to get around the security of specific targets and evade detection by gathering details through phishing emails that look convincingly similar to company emails. They may focus more time exploiting accounts with privileged access but will not pour too much time into a target.
- Level 3 aims to protect from attackers who exploit vulnerabilities in old hardware or software and avoid detection when accessing your systems. Such attackers often focus on specific targets and leverage techniques outside of publicly accessible platforms. To continue the phishing email example: these attackers will socially engineer someone to click on a link and then may continue manipulating them for information on bypassing security undetected.
Each of these levels focuses on different types of cyber security threats. The higher the number, the more protection you have against sophisticated attacks.
A managed security services provider (MSSP) can evaluate your software and systems to find these vulnerabilities. From there, they can place your organisation within one of the four maturity levels and highlight what you need to improve your cyber security posture.
The Essential Eight’s threat reduction strategies
Once you have established your maturity level and the vulnerabilities within your organisation, you need to address them with the Essential Eight.
It is pertinent to note that each of these categories requires you to meet specific criteria before reaching a maturity level in that area. For example, application control at maturity level one blocks actions within apps, but you need to implement Microsoft’s recommended block rules to achieve maturity level three.
So, the summary of the strategies below merely describes the general safeguards they cover and not the specific requirements to meet each maturity level.
The eight strategies covered in the cyber security model include:
- Application control restricts the actions someone can execute in a users’ application. It especially prevents workstations from running software libraries, scripts, application installers, HTML applications, etc.\
- Application patching includes the time to patch vulnerabilities in third-party applications. After an application updates, you need to patch it within two weeks or 48 hours if it has a known vulnerability. You need a vulnerability scanner to detect missed patches or potential issues.
- Configure Microsoft Office macro settings to prevent anyone without a demonstrated business requirement from accessing macros. Macros are commands grouped to complete a task automatically. Your cyber security solution should block macros in files from the internet, prevent users from changing security settings and leverage antivirus scanning.
- User application hardening tightens the capabilities of web browsers so they cannot process Java or web advertisements from the internet, and users cannot change the security settings.
- Restricting administrative privileges ensures that people with privileged access use different operating environments from unprivileged users. Administrators need to have a permission request validated before accessing these environments.
- Patch operating systems to ensure they remain updated. You should do this within two weeks of the update or 48 hours if the operating system has a known vulnerability. Like application patching, you need regular vulnerability scanning to identify potential issues within the operating system.
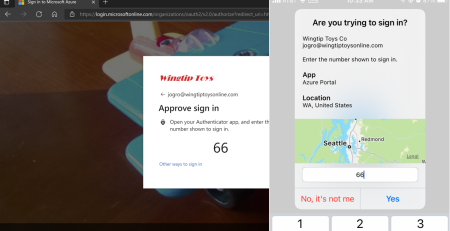
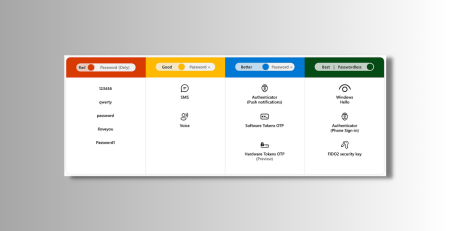
- Multi-Factor Authentication (MFA) will need to be leveraged by all end-users to guard against security breaches such as brute force attacks. All internet-facing services that store and access sensitive information need MFA enabled.
- Regular backups ensure that you can access your systems and data in the event of a cyber security attack. You need to test your backup systems and environments to ensure they meet your disaster recovery needs. Unprivileged accounts can only access their own backups and cannot delete data.
How Alliance Business Technologies secures your business
We build systems designed to protect your critical assets. We increase business resilience, provide real-time threat intelligence, and help create a robust cyber security culture.
Our advisory services can help you pinpoint your risks and provide visibility of your cyber security posture. We can implement monitoring systems to notify you of potential threats and provide solutions before they cause damage to your organisation. Finally, we can provide your employees with training to recognise threats, protecting themselves and the business.
Visit our IT Security page for more on how we protect your business, your customers, and their data.
Article used with permission from Centorrino Technologies.