Improving security posture by blocking legacy authentication
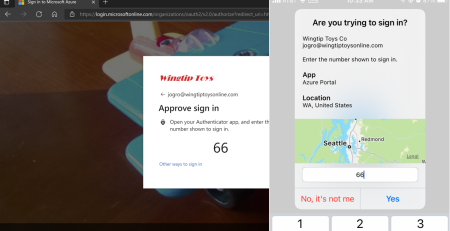
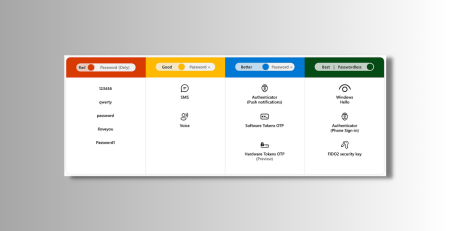
We have spoken to you about Multi-Factor Authentication and it is good to see so many of our clients are taking MFA seriously and are using to keep their data safe. But sometimes we still see user accounts being compromised. How is that possible? The main culprit here is older software. Applications that can’t use the benefits of modern authentication can’t be safe, unless we simply deny access. Think of older versions of Office, or older email applications on your smartphone. The only remedy here is to stop using the older software, and have us turn off any access that is using these systems.
When MSPs refer to ‘Legacy Authentication’, we’re talking about old user authentication protocols that were previously used by Office clients 2010 and older. Microsoft started fazing these protocols out in September 2019 in attempts to wean users off of sending usernames and passwords, often stored on or saved to devices.
Why was this change important?
- Older Microsoft Office apps and apps using mail protocols like POP, SMTP, IMAP, and MAPI can’t enforce MFA, making them the preferred entry points for adversaries attacking your organization.
What do I do if I have older apps with Legacy Authentication?
- To prepare for legacy authentication you must ensure that everyone in your business meets and understands these requirements
- Use only Android Phone version 9 or higher: If you have an Android phone, you must use Android version 9 or higher. Modern iOS (Apple) is okay.
- Use Outlook mail app: Email applications other than the Outlook app may not work after the changes are completed.
- Ensure Office is the most current version
- Ensure Line of Business applications are up to date and compatible with modern authentication. It is up to the third-party provider to ensure compatibility and resolve the issues.
Find out more!
Talk to us about making sure your data is safe by disabling legacy authentication.
For more information please watch the video below:
Article used with permission from The Technology Press.